A widespread attack method used by cybercriminals is compromising (business) emails. For example, users receive an email from a supervisor, manager, or other authority with a request to forward sensitive data, click on a link, or open a file. Although the email is by no means from the purported sender, users are more inclined to open the files or click on the link since it appears so.
Table of Contents
Phishing at Microsoft Teams, Slack, and Co.
Cybercriminals are extremely sophisticated, using pictures of supervisors, deep fakes, or chats on platforms such as Slack and Teams. These attacks are not limited to emails but to various channels and social networks used in the business environment. Deep fakes can even be used to fake a person’s voice and use it in video conferences. Many users have little idea of the phishing threats lurking today, let alone how best to respond. Training that addresses exactly this is an important pillar for corporate security.
Training Helps To Better Protect Networks And Fight Malware
Users should be able to recognize when emails or other messages are not legitimate, even if the sender is supposed to be a manager or other authority figure. However, it is not easy. But users should learn not to blindly open a file or click a link just because the sender appears familiar. Training forms an important foundation for reliably recognizing such emails and what to do if a suspicious email arrives in the mailbox. Fake invoices and documents of this type are also often sent by email to lure recipients into a trap or inject malware. Cybercriminals are now extremely sophisticated. Without appropriate education and training, employees often react incorrectly.
More QR Scams And QR phishing
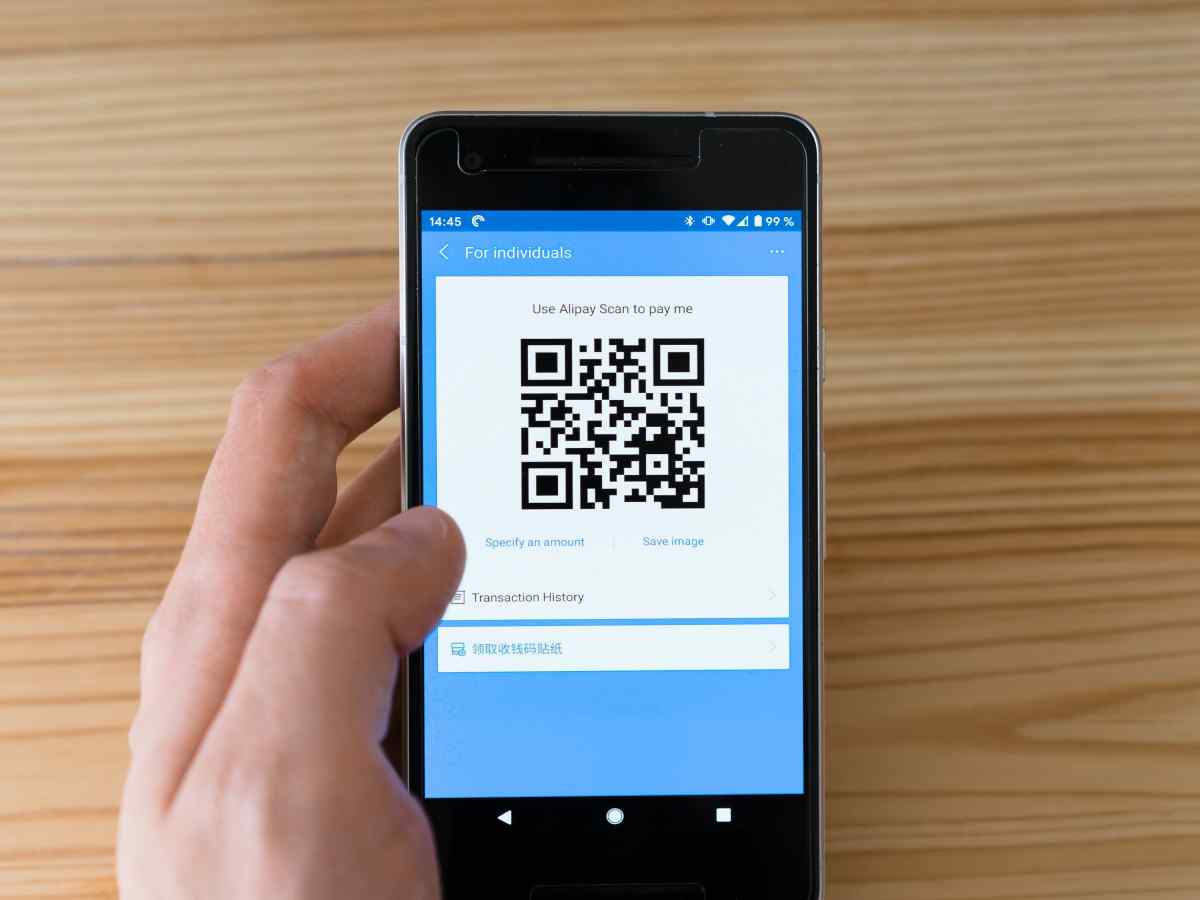
QR scams direct users to compromised websites. QR codes entice users to quickly and easily access websites on their smartphones by scanning the code. Statistics show that nearly 90 percent of smartphone users have scanned at least one QR code, with over a third doing so weekly. With some delay, QR codes are now spreading in many areas. So users should know how they work and what to look out for when using them.
QR codes are also used in phishing attacks. To do this, the attackers integrate QR codes into phishing emails or other messages. After scanning, a new website opens, and the user is prompted to enter his username and password, for example. Cybercriminals use this technique to undermine the security functions of the email system: it does not recognize the dangerous URLs because the email only contains a QR code. Users should know this and be more careful with QR codes or become suspicious of suspicious QR codes.
Deep Fakes Combined With Spear Phishing
Deep fakes are deceptively real-looking videos or images. They are often used for targeted disinformation or in the field of social engineering. Deep fakes are often difficult to detect but pose a growing threat. They are often used with spear phishing attacks to extract information from the victim specifically. Even if deep fakes are well done, the message is often implausible, or the image/video itself seems inconsistent. What you have to pay attention to can be trained well with the help of professionals. There are now deep fakes in the form of calls. Deep fakes over the phone are often based on text-to-speech technologies combined with the perfect voice fake. Such deep fakes are now able to
Mobile Security
More and more users work primarily on the go on notebooks, tablets, or smartphones. Many mistakenly rely on the security of their smartphones and take phishing attacks or malware on mobile devices less seriously than on a stationary computer. In the prevailing, at least hybrid, work models, employees access corporate networks via various mobile channels. Fake apps and fake URLs are spreading rapidly, creating an additional gateway for cybercriminals. Virus scanners offer little protection. Prudent operation and the right reaction are better in a cyber attack. The almost nationwide switch to remote working or hybrid infrastructures has opened up numerous gateways. This is where training often works wonders.
Cyber Attacks From Within: Insider Threats
Unsurprisingly, company networks are threatened by unknown external attackers and insiders from their own companies. These can be dissatisfied employees, criminals who have been smuggled in, guests, partners, or suppliers. There are many ways to become part of the company, attack it internally, and defeat most external security systems. If employees spy on other employees or try to access data, it is naturally more difficult to counteract abuse. Users should know how to protect their data and ensure that only authorized persons can access their respective computers.
Conclusion
Networks are already vulnerable, and untrained users increase the potential for privacy and data security breaches. Phishing is one of the most pervasive cyber threats, and there are countless ways that phishing can be used to obtain sensitive information. However, companies and users are not defenseless against this. The probability of a successful attack can be significantly reduced through targeted, practical security awareness training.